Always Encrypted in SQL Server: The Definitive Guide to End-to-End Data Protection, Zero-Trust Architecture, and Regulatory Compliance
Introduction: Data Is the New Liability
In the digital economy, data is no longer just an asset.
It is a liability.
Every organization stores personally identifiable information (PII), financial records, health data, trade secrets, authentication credentials, and operational intelligence. A single breach can result in:
- Multi-million-dollar regulatory fines (GDPR, LGPD, HIPAA, PCI-DSS)
- Irreversible reputational damage
- Class-action lawsuits
- Loss of customer trust
- Executive accountability
The modern threat landscape is not limited to external attackers. Insider threats, compromised administrative accounts, memory scraping, backup theft, and lateral movement attacks are now common breach vectors.
Traditional perimeter security is no longer sufficient.
This is where Always Encrypted in SQL Server becomes strategically critical.
It is not merely a feature.
It is a fundamental shift toward a zero-trust data model.
What Is Always Encrypted?
Always Encrypted is an end-to-end encryption technology introduced in SQL Server 2016 and continuously enhanced in later versions and Azure SQL.
Unlike Transparent Data Encryption (TDE), which protects data at rest, Always Encrypted protects sensitive data:
- At rest
- In transit
- In memory
- During query execution
Most importantly:
The SQL Server engine never sees the plaintext data.
Encryption and decryption occur entirely on the client side.
This architectural decision changes everything.
Why TDE Is Not Enough
Transparent Data Encryption protects:
- Data files
- Log files
- Backups
It prevents someone from attaching a stolen database file to another server.
However, TDE does NOT protect against:
- Privileged DBAs reading sensitive columns
- SQL injection extracting data
- Compromised service accounts
- Memory dump analysis
- Insider abuse
- Elevated privilege attacks inside the environment
TDE secures storage.
Always Encrypted secures exposure.
They solve different problems.
The Core Principle: Client-Side Encryption
Always Encrypted enforces cryptographic separation between:
- Data storage (SQL Server)
- Key ownership (trusted key store)
- Decryption capability (authorized client application)
The SQL Server instance only processes encrypted binary values.
This means:
- DBAs cannot read sensitive data
- Database backups reveal nothing
- Memory inspection reveals ciphertext
- Query logs contain encrypted values
- Even sysadmin-level accounts cannot bypass encryption
This aligns directly with Zero Trust Architecture principles.
Trust is not assumed — not even internally.
How Always Encrypted Works (Technical Deep Dive)
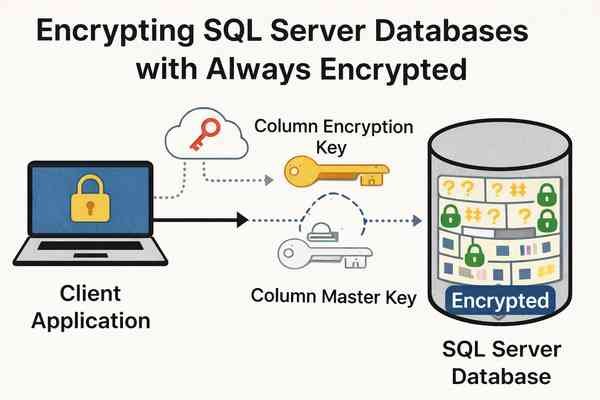
Always Encrypted operates using a hierarchical key architecture:
1. Column Master Key (CMK)
The Column Master Key protects the encryption keys.
It is stored outside SQL Server in a trusted key store, such as:
- Windows Certificate Store
- Azure Key Vault
- Hardware Security Modules (HSM)
- Managed HSM in Azure
The CMK never resides inside the database engine.
2. Column Encryption Key (CEK)
The CEK encrypts the actual data in table columns.
The CEK is stored inside SQL Server metadata — but encrypted using the CMK.
This creates cryptographic separation between data and key ownership.
Query Execution Flow
When an application sends a query:
- The client driver (ADO.NET, ODBC, JDBC) detects encrypted columns.
- The driver retrieves metadata about encryption.
- The driver decrypts parameters locally using the CMK.
- Encrypted parameters are sent to SQL Server.
- SQL Server processes only ciphertext.
- Results are returned encrypted.
- The client decrypts results locally.
SQL Server never processes plaintext.
This design dramatically reduces data exposure risk.
Deterministic vs Randomized Encryption
Always Encrypted supports two encryption modes:
Deterministic Encryption
- Produces the same ciphertext for the same plaintext
- Allows equality comparisons
- Supports indexing
- Enables JOIN and WHERE operations
Best for:
- National IDs
- Social Security Numbers
- Account numbers
Trade-off:
- Slightly less resistant to pattern analysis
Randomized Encryption
- Produces different ciphertext for the same plaintext
- Maximum confidentiality
- No equality comparison possible
Best for:
- Highly sensitive personal data
- Financial values
- Medical information
Trade-off:
- Limited query capabilities
Choosing the correct mode requires architectural planning.
Real-World Use Cases
Always Encrypted is ideal for:
- Credit card numbers
- Social Security / National ID numbers
- Bank account details
- Medical records
- Salary information
- Legal case data
- Authentication tokens
It is especially critical in:
- Financial services
- Healthcare systems
- Government databases
- SaaS platforms handling multi-tenant data
Regulatory Compliance and Legal Strategy
Modern regulations demand:
- Data minimization
- Access control
- Encryption at rest and in transit
- Role-based visibility
- Auditability
Always Encrypted supports compliance frameworks including:
- GDPR (European Union)
- LGPD (Brazil)
- HIPAA (United States)
- PCI-DSS (Payment Card Industry)
- ISO 27001
More importantly, it supports defensible security posture.
If a breach occurs, encrypted data that cannot be decrypted may not legally qualify as exposed data under certain regulatory frameworks.
That distinction can mean millions in avoided fines.
Performance and Architectural Considerations
Always Encrypted is powerful — but not free.
Consider:
- Increased storage footprint
- Limited search capabilities
- Potential index restrictions
- Client driver compatibility requirements
- Key management complexity
Best practices include:
- Encrypt only truly sensitive columns
- Benchmark performance impact
- Design queries carefully
- Plan key rotation strategy
- Use Azure Key Vault for enterprise key governance
Security must be balanced with operational efficiency.
Always Encrypted with Secure Enclaves (Advanced Topic)
SQL Server 2019 introduced Always Encrypted with Secure Enclaves.
This enhancement allows:
- Pattern matching
- Range queries
- Richer comparisons
- In-place encryption changes
All executed inside a protected enclave within the server environment.
Secure Enclaves reduce functional limitations while preserving encryption guarantees.
For advanced enterprise workloads, this feature significantly expands applicability.
The Zero-Trust Security Model
Always Encrypted embodies Zero Trust principles:
- Assume breach
- Minimize data exposure
- Separate duties
- Restrict privileged visibility
- Enforce least privilege access
It protects against:
- Insider threats
- Credential compromise
- Privileged abuse
- Backup theft
- Memory scraping attacks
It shifts the security perimeter from infrastructure to data itself.
That is a strategic evolution.
Key Management: The Real Responsibility
Encryption is only as strong as key governance.
Best practices:
- Store CMKs in Azure Key Vault or HSM
- Enable role-based access control
- Enforce multi-factor authentication
- Implement key rotation policies
- Audit key access logs
- Protect certificate backups offline
Key compromise equals data compromise.
Operational maturity is mandatory.
When Should You Use Always Encrypted?
Use Always Encrypted when:
- Regulatory compliance requires strict confidentiality
- DBAs should not access specific data fields
- Multi-tenant SaaS isolation is required
- Sensitive financial or medical data is stored
- Zero-trust architecture is desired
Do NOT use Always Encrypted when:
- Full-text search on encrypted columns is required
- Heavy analytical workloads require plaintext processing
- The application cannot support compatible drivers
Architecture must precede implementation.
Strategic Conclusion: Encryption Is a Leadership Decision
Implementing Always Encrypted is not just a technical configuration.
It is a statement.
It declares that:
- Data privacy is non-negotiable
- Insider threats are real
- Zero trust is necessary
- Security is proactive, not reactive
TDE protects files.
Always Encrypted protects trust.
In a world where data breaches are inevitable, the question is not whether you will be attacked.
The question is whether your data will be readable when it happens.
Always Encrypted ensures that even if infrastructure fails, credentials are stolen, or backups leak —
Your most sensitive information remains cryptographically shielded.
And in modern cybersecurity strategy, that difference is everything.
🚀 Ready to boost your career in data?
👉 DBAcademy – DBA & Data Analyst Training
Over 1,300 lessons and 412 hours of exclusive content.
Includes subtitles in English, Spanish, and French.
🔗 https://filiado.wixsite.com/dbacademy
💡 Start learning today and become a highly in-demand data professional.
Share this content:


Post Comment